Certified Virtualization Security Expert, Part 5 of 6: Hardening the Server
with experts Duane Anderson, Tim Pierson
Course description
This course is about the hardening techniques of the ESX server. It will cover best practices, isolation, and how templates can be used effectively. It will also cover VM segmentation, limiting data flow, the setinfo hazard, directory services control access and maintaining logs.
Prerequisites
This is part 5 of the series
Learning Paths
This course will help you prepare for the following certification and exam:
Certified Virtualization Security Expert
Meet the experts
Duane has been working in the IT industry for over two decades. He has primarily focused on security related matters such as
Penetration Testing and Forensics. He has appeared as an expert witness
in multiple court hearings on IT related matters. Duane has worked for
or with most US and some foreign military branches, U.S government
agencies, banking and regulatory industries and Fortune 500 companies.
Duane contributed to the coordination and execution of IT
counter-hacking & security courses for the US Marine Corps, US Army,
US Air Force, U.S. Treasury, Sprint, IBM, Washington Mutual and Service
Canada.
Tim one of the World’s leading trainers in technology,
networks, virtualization and, applications. He has been a technical trainer and consultant for security and virtualization for the past 25 years. He has 29 industry technical certifications from CISCO, Microsoft and Novell. Tim has been a noted speaker at many industry events such as Infosec World 2010, Innatech and GISSA. He is a contributing author of VMware vSphere and Virtual Infrastructure Security Securing ESX in the Virtual Environment.
networks, virtualization and, applications. He has been a technical trainer and consultant for security and virtualization for the past 25 years. He has 29 industry technical certifications from CISCO, Microsoft and Novell. Tim has been a noted speaker at many industry events such as Infosec World 2010, Innatech and GISSA. He is a contributing author of VMware vSphere and Virtual Infrastructure Security Securing ESX in the Virtual Environment.
Course outline
Hardening
Hardening VMs (31:24)
- Introduction (00:27)
- Virtual Machines (01:40)
- Disable Unnecessary or Superfluous Functions (01:49)
- Templates (00:57)
- Prevent VMs from Taking Over Resources (01:59)
- Isolate VM Networks (00:49)
- Example Network Architecture (02:29)
- ARP Cache Poisoning (02:13)
- Virtual Machine Segmentation (03:38)
- Disable Copy and Paste Operations (01:07)
- Limit Data Flow (01:50)
- Limit Data Flow Continued (01:38)
- SetInfo Hazard (00:59)
- SetInfo Hazard Continued (01:11)
- Non-Persistent Disks (01:22)
- Persistent Disks (02:42)
- Ensure Unauthorized Devices are Not Connected (02:10)
- Avoid DoS caused by Virtual Disk Modification (02:05)
- Summary (00:08)
Verify File Permissions (31:16)
- Introduction (00:08)
- Verfiy File Permissions (02:16)
- Demo: Graph (02:02)
- Demo: Virtual System Center (06:09)
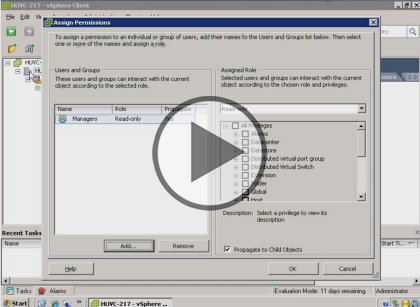
- Demo: Assign Permissions (03:52)
- Demo: Permissions Continued (05:35)
- Demo: User Permissions (04:55)
- Demo: XP-Attacker (05:47)
- Configuring ESX and ESXi (00:19)
- Summary (00:08)
The Service Console
Configure Service Console and Firewall (41:39)
- Introduction (00:08)
- Configuring the Service Console in ESX (02:30)
- Demo: Set up ESX Access (05:17)
- Demo: Checking Access (03:54)
- Demo: Users and Groups (05:36)
- Demo: esxadmins (04:55)
- Configure the Firewall for Maxium Security (02:14)
- Demo: Firewall Services (05:19)
- Demo: Reading Firewall Information (05:30)
- Demo: Turn off Unnecessary Ports (04:57)
- Limiting Running Services (01:05)
- Summary (00:08)
Service Console (30:34)
- Introduction (00:08)
- Limit What's Running in the Service Console (01:26)
- Processes Running in SC (01:12)
- The vSphere Client (03:51)
- Use a Directory Service for Authentication (03:03)
- Demo: Active Directory Integration (05:21)
- Demo: Enable the Domain (04:15)
- Demo: Authentication (03:03)
- Demo: No Password Account (05:13)
- Root (02:49)
- Summary (00:08)
Controlling Access
Control Access (32:56)
- Introduction (00:08)
- Strictly Control Root Privileges (02:32)
- Control Access to Privileged Capabilities (02:33)
- Demo: Hardening ESX (05:33)
- Demo: sshd-config (05:14)
- Demo: Special User Permissions (05:12)
- Demo: User vs. Group Permissions (06:00)
- Demo: Successful Login (05:33)
- Summary (00:08)
Control Access Part 2 (35:16)
- Introduction (00:08)
- Demo: Banner (02:11)
- Demo: Other Commands (04:10)
- Demo: Implementing sudo (04:48)
- Demo: Changes for sudo (04:59)
- Demo: sudoers File (05:08)
- Demo: Sudo Changes (05:11)
- Demo: Run Commands as Another User (04:22)
- Demo: Running Commands Continued (03:12)
- Password Aging and Complexity (00:54)
- Summary (00:08)
Hardening ESX and ESXi
Configure ESX (39:03)
- Introduction (00:08)
- ESX/Linux User Authentication (01:17)
- Configuring ESX Authentication (01:30)
- ESX Authentication Settings (01:50)
- Reusing Passwords (01:54)
- Configuring Password Complexity (03:32)
- Managing ESX (00:45)
- Maintain Proper Logging (03:00)
- Best Practices for Logging (01:38)
- ESX Log Files (01:17)
- Establish and Maintain File System Integrity (03:16)
- SNMP (01:11)
- Protect Against the Root File System Filling Up (01:18)
- Disable Automatic Mounting of USB Devices (01:23)
- Isolation (05:16)
- VLAN1 (01:11)
- Encryption Issues (03:31)
- Do Not Use Promiscuous Mode on Network Interfaces (00:55)
- Protect Against MAC Address Spoofing (02:51)
- Protect Against Network Attacks (01:04)
- Summary (00:08)
Hardening an ESXi Server (16:49)
- Introduction (00:28)
- Differences: VMware ESX and ESXi (01:15)
- Configure Host-Level Management (00:23)
- Strictly Control Root Privileges (01:22)
- Control Access to Privileged Capabilities (00:53)
- Control Access to Privileged Capabilities Cont. (01:58)
- Privilege Levels (00:49)
- DCUI (00:48)
- DCUI Continued (01:42)
- Maintain Proper Logging (01:03)
- Establish and Maintain ConfigFile Integrity (01:32)
- Secure the SNMP Connection (01:40)
- Ensure Secure Access to CIM (00:56)
- Audit or Disable Technical Support Mode (01:45)
- Summary (00:08)