Course description
In the SQL Server 2014: Permissions and Data Protection course you will understand permissions in SQL Server and how they provide granular control over data and objects. Then you will learn how to provide a final layer of defense by encrypting data.
Prerequisites
This course assumes that you have at least a basic familiarity with the concept of relational databases and a basic understanding of what SQL Server is and the high-level tools in it, as well as how to create and manage objects using Management Studio.
Learning Paths
This course will help you prepare for the following certifications and exams:
MCSE: Business Intelligence
MCSA: SQL Server 2012/2014
MCSE: Data Platform
70-462: Administering Microsoft SQL Server 2012/2014 Databases
70-461: Querying Microsoft SQL Server 2012/2014
This course is part of the following LearnNowOnline SuccessPaths™:
SQL Server Core
Meet the expert
Don Kiely is a featured instructor on many of our SQL Server and Visual Studio courses. He is a nationally recognized author, instructor, and consultant specializing in Microsoft technologies. Don has many years of teaching experience, is the author or co-author of several programming books, and has spoken at many industry conferences and user groups. In addition, Don is a consultant for a variety of companies that develop distributed applications for public and private organizations.
Course outline
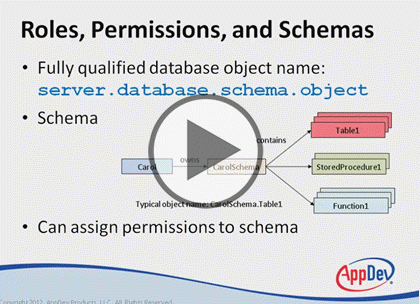
Permissions, Schemas, Metadata
Permissions (19:28)
- Introduction (00:41)
- Permissions (01:25)
- Permission Types (04:15)
- Permission Statements (02:01)
- Summary (00:38)
- Default Schemas for Users (00:53)
- Demo: How Schemas Work (07:18)
- Default Schemas for Groups (00:49)
- Demo: Potential Problems (06:40)
Default Schemas (17:15)
- Introduction (00:52)
- Default Schemas for Users (00:53)
- Demo: How Schemas Work (07:18)
- Default Schemas for Groups (00:49)
- Demo: Potential Problems (06:40)
- Summary (00:41)
Execution and Metadata (21:30)
- Introduction (00:44)
- Execution Context (02:23)
- Ownership Chaining (01:13)
- Changing the Execution Content (04:14)
- Demo: Execution content (06:25)
- Metadata Security (01:57)
- Demo: Permissions and Metadata (04:17)
- Summary (00:13)
Encryption
Data Encryption (21:29)
- Introduction (00:35)
- Data Encryption (03:28)
- Encryption Keys (04:33)
- Demo: How Encryption Works (10:30)
- Key Management (01:48)
- Summary (00:32)
Encrypting Data (30:48)
- Introduction (00:40)
- Demo: Table Creation (01:59)
- Demo: Certificate Keys (08:45)
- Demo: Asymmetric Keys (07:46)
- Demo: Symmetric Keys (10:10)
- Summary (01:26)