Course description
In this course you’ll look at building secure applications from the mindset of the hacker and what a developer can do to avoid the front pages of the latest exploit. You will see examples of Cross-Site Forgery, how a phishing email works, the vulnerabilities of open source components, and also redirects from unvalidated links.
Prerequisites
This course is for users with experience with developing web applications using C# or other object oriented programming languages.
Learning Paths
This course is part of the following LearnNowOnline SuccessPaths™:
OWASP
Meet the expert
Mike Benkovich delivers technical presentations around the U.S. as a consultant, trainer, and former Developer Evangelist for Microsoft. He has worked in a variety of professional roles including architect, project manager, developer, and technical writer. Mike is also an author of two books, published by WROX Press and APress, that show developers how to get the most from their SQL databases. Since appearing in the 1994 Microsoft DevCast, Mike has presented technical information at seminars, conferences, and corporate boardrooms across America.
Course outline
OWASP Addtional Topics
Cross-Site Request Forgery (15:23)
- Introduction (00:22)
- Cross-Site Request Forgery (00:45)
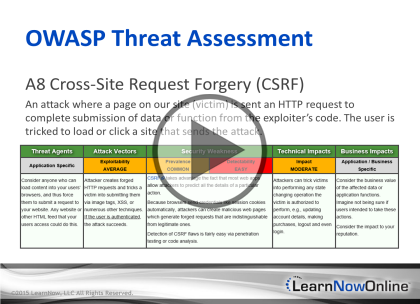
- OWASP Threat Assessment (01:08)
- Example (01:17)
- Phishing Email Sent to User... (00:29)
- Code Includes CSRF Hack (00:20)
- CSRF (00:28)
- Demo: CSRF (06:02)
- Demo: Preventing CSRF (02:31)
- Cross-Site Request Forgery (01:42)
- Summary (00:14)
Vulnerable Components (12:39)
- Introduction (00:23)
- Known Vulnerabilities (00:43)
- Example: Apache CXF & Spring (00:38)
- OWASP Threat Assessment (01:46)
- Components Known Vulnerabilities (00:44)
- Reality of Software Components (01:27)
- Explained... (00:51)
- Comps with Known Vulnerabilities (00:38)
- Demo: Known Vulnerabilities (05:07)
- Summary (00:18)
Redirects (11:56)
- Introduction (00:30)
- Unvalidated Redirects (02:41)
- Example (00:18)
- Demo: Unvalidated Redirects (05:55)
- Demo: Using Validation (01:20)
- Unvalidated Redirects (00:55)
- Summary (00:15)