Course description
So you’d like to become a computer forensic investigator. Where do you start? Dive into computer forensic basics to establish a solid foundation, starting with answers to the questions of what is computer forensics, why do we need it, and when should we use it? Explore the various categories of cybercrimes and the laws that pertain to them, learn how to begin the investigation process, and get a quick look at forensic readiness and some resources that are available to forensic investigators. This course is part of a series covering the EC-Council Computer Hacking Forensic Investigator (CHFI).
Prerequisites
Recommended:
Understanding of networking; How data flows from source and destination
Computer security basics such as passwords, encryption and physical security
Basic understanding of computing and computer systems
Experience with various operating systems
Learning Paths
This course will help you prepare for the following certification and exam:
Computer Hacking Forensic Investigator
Meet the expert
David Bigger is the lead trainer at Bigger IT Solutions. He has been information technology for a little over 20 years and has been training all over the US. He has worked with companies like US Military, Lockheed Martin, General Dynamics, Dominos Pizza, University of Utah and Expedia
Course outline
Computer Forensics Basics
Forensics Introduction (34:43)
- Introduction (00:24)
- What Is Computer Forensics? (04:40)
- Why Computer Forensics? (02:25)
- When Do You Need Computer Forensics? (02:55)
- Categories of Cyber Crimes (03:46)
- Challenges (05:27)
- Investigation Process (02:44)
- Internal or Administrative Investigation (03:07)
- Civil vs. Criminal (02:26)
- Rules/Keys of Forensic Investigation (04:18)
- Enterprise Theory of Investigation (02:11)
- Summary (00:15)
Evidence (24:45)
- Introduction (00:28)
- Digital Evidence (01:14)
- Types of Digital Evidence (01:55)
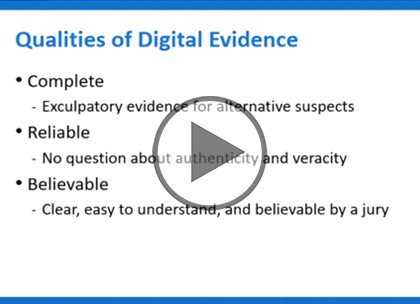
- Qualities of Digital Evidence (03:00)
- Why Do We Need Digital Evidence (02:28)
- Sources of Potential Evidence (05:22)
- Rules of Evidence (01:08)
- Best Evidence Rule (02:34)
- Federal Rules of Evidence (01:32)
- Hearsay Rule (01:48)
- Hearsay Rule Exceptions (02:54)
- Summary (00:17)
Forensic Readiness (23:05)
- Introduction (00:26)
- Forensic Readiness (04:09)
- Forensic Readiness Checklist (02:58)
- Why a Forensics Investigator? (01:52)
- Forensic Investigator Responsibilities (01:52)
- Making a Forensic Investigator (04:51)
- Privacy Issues (01:41)
- Code of Ethics (03:22)
- Forensic Workgroups (01:31)
- Summary (00:20)