Course description
Hacking has gone from an obscure term to something that appears in the daily news. In this course we'll get started with what is hacking and understand some of the differences between "white hat" hackers and "black" or "grey" hat hackers. It will cover at a high level what are some of the essential tools a hacker needs to know about and be proficient with as well as the credentials of a hacker and what you can expect when becoming a Certified Ethical Hacker (CEH), an certification by the EC-Council.
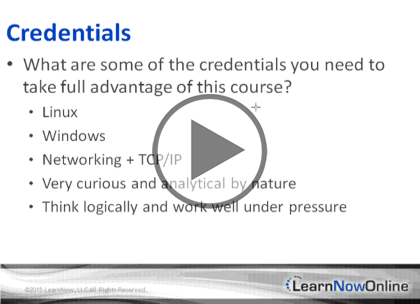
Prerequisites
To get the most out of this course, this course assumes that you have a good working knowledge of Linux and Windows based networking environments. It also assumes that you have experience with managing a network, have worked with networking hardware such as switches & routers, are familiar with MS Active Directory (AD) Domain based authentication, know how to work with command-line utilities, and understand the basics of Web Server environments.
Many of the demonstrations in this course use the Windows 7 and Kali Linux operating systems which can be downloaded free from the respective sites. All of the demonstrations are created in a virtual environment using Oracle VirtualBox and VMware vSphere 6.
Learning Paths
This course will help you prepare for the following certification and exam:
Certified Ethical Hacker
312-50: Certified Ethical Hacker
Meet the expert
Rafiq Wayani has extensive experience including more than 20 years in IT as Systems Architect, Software Engineer, DBA, and Project Manager. Wayani has instructed in a variety of technical areas, has designed and implemented network and information systems, and is certified across a wide range of platforms and systems including Microsoft Solutions Developer, Systems Engineer, Application Developer, Database Administrator, Trainer; Novell Netware Administrator and Engineer; Master Certified Netware Engineer; and A Certified.
Course outline
Intro to Ethical Hacking
Introduction (20:27)
- Introduction (00:16)
- Certified Ethical Hacking (00:56)
- Introduction (18:59)
- Summary (00:14)
Hacker Credentials (21:40)
- Introduction (00:18)
- Credentials (09:15)
- Demo: Wizard vs. Cmd Line (06:33)
- Demo: PowerShell (05:17)
- Summary (00:15)
Hacker Credentials Part 2 (07:14)
- Introduction (00:23)
- Credentials (00:21)
- OSI Model (03:52)
- Credentials Cont. (00:28)
- Demo: Linux (01:56)
- Summary (00:10)
Being a Hacker (06:01)
- Introduction (00:22)
- What Is It Like? (01:03)
- Demo: Understand the System (03:05)
- What Is It Like? Cont. (01:19)
- Summary (00:10)
Footprinting and Reconnaisance
Terminology (14:58)
- Introduction (00:21)
- Terminology (07:24)
- Terminology Cont. (06:57)
- Summary (00:14)
Tools (11:01)
- Introduction (00:27)
- Tools (02:53)
- Demo: Basic Windows Script (02:30)
- Demo: Basic Linux Script (02:38)
- Demo: Differences (02:15)
- Summary (00:15)
Footprinting (17:42)
- Introduction (00:17)
- Footprinting & Reconnaissance (05:36)
- Active & Passive Footprinting (04:55)
- Footprinting Sources (01:14)
- Demo: Google Hacking (01:38)
- Demo: Other Online Tools (02:34)
- Footprinting Sources Cont. (01:15)
- Summary (00:10)
Footprint Tools and CM (12:43)
- Introduction (00:15)
- Types of Information Gathered (06:36)
- Methods Available (02:13)
- Mitigate Footprinting (03:26)
- Summary (00:11)