Certified Information Security Manager CISM, Part 4 of 4: Incident Management
with expert Kenneth Mayer
Course description
This course talks about different parts of incident management, overview, organization, resources, ways of measuring it, procedures, current state of incident response capability, and how to develop an incident response plan. You will also learn how to coordinate with disaster recovery and responsibility and discovery plans and testing. It wraps up with a post incident activities investigation. This course is part of a series covering the ISACA Certified Information Security Manager (CISM).
Prerequisites
This is part 4 in the series
Learning Paths
This course will help you prepare for the following certification and exam:
Certified Information Security Manager
Meet the expert
As a certified Microsoft Instructor, Ken has focused his career on various security aspects of computer and network technology since the early 1980s. He has offered a wide variety of IT training and high level consulting projects for Fortune 500 companies globally. Through the course of his extensive career, he has taught a full line of Microsoft, CompTIA, Cisco, and other high level IT Security curricula.
Course outline
Introduction to Incident Management
Incident Management Overview (28:43)
- Introduction (00:53)
- Introduction to Incident Management (03:09)
- Incident Management Overview (03:44)
- Types of Events (02:43)
- Types of Events Continued (03:21)
- Goals of Incident Management (04:45)
- BCP and DRP (06:31)
- Goals of Incident Management Continued (03:25)
- Summary (00:08)
Incident Response Procedures (29:28)
- Introduction (00:24)
- Introduction to Incident Response Planning (03:40)
- Importance of Incident Management (08:01)
- Outcomes of Incident Management (03:51)
- Incident Management (01:34)
- Concepts (03:44)
- Concepts Continued (01:35)
- Incident Response (01:34)
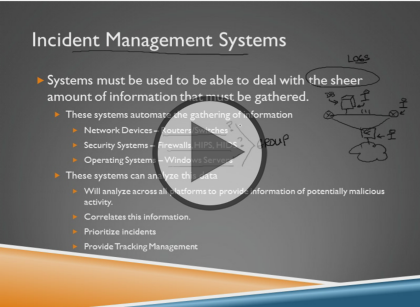
- Incident Management Systems (04:54)
- Summary (00:08)
Incident Management Organization and Resources
Incident Management Organization (18:54)
- Introduction (00:21)
- Introduction to Incident Management Organization (02:59)
- Incident Management Organization (02:30)
- Responsibilities (03:44)
- Responsibilities Continued (02:58)
- Defining Security Incidents (05:10)
- Senior Management Commitment (01:01)
- Summary (00:08)
Incident Management Resources (36:18)
- Introduction (00:26)
- Policies and Standards (00:37)
- Incident Response Technology Concepts (11:11)
- Personnel (03:11)
- Roles and Responsibilities (08:24)
- Skills (08:09)
- Awareness and Education (01:21)
- Audits (02:48)
- Summary (00:08)
Incident Management Objectives (13:58)
- Introduction (00:18)
- Defining Objectives (00:48)
- The Desired State (03:29)
- Strategic Alignment (06:42)
- Other Concerns (02:31)
- Summary (00:08)
Incident Management Metrics and Indicators (13:03)
- Introduction (01:06)
- Defined Responsibilities (03:01)
- Management Metrics and Monitoring (01:35)
- Metrics and Minitoring Continued (02:48)
- Other Things to Monitor (04:23)
- Summary (00:08)
Current State of Response Capability (11:15)
- Introduction (00:12)
- Threats (04:39)
- Vulnerabilities (06:15)
- Summary (00:08)
Incident Response Plan
Developing an Incident Response Plan (31:44)
- Introduction (00:45)
- Elements of an Incident Response Plan (08:21)
- Gap Analysis (03:04)
- BIA (05:05)
- BIA Continued (02:48)
- Escalation Process for Effective IM (02:45)
- Identifying Security Incidents (01:27)
- Incident Management and Response Teams (02:10)
- Organizing, Training, and Equipping Response Staff (01:55)
- Incident Notification Process (00:55)
- Incident Management Plan Challenges (02:17)
- Summary (00:08)
Recovery Options (30:02)
- Introduction (01:33)
- Goals of Recovery Operations (04:00)
- Mobile Sites (05:37)
- Choosing a Site Selection (01:18)
- Recovery Plan (03:58)
- Incident Management Response Teams (02:10)
- Network Service High Availability (04:16)
- Storage High Availability (04:01)
- Risk Transference (01:27)
- BCP and DRP (01:28)
- Summary (00:08)
Testing Response and Recovery Plans (10:26)
- Introduction (02:18)
- Periodic Testing (01:17)
- Testing IT Infrastructure (02:05)
- Analyze Test Results (03:39)
- Measuring the Test Results (00:56)
- Summary (00:08)
Executing the Plan (25:38)
- Introduction (01:57)
- Updating the Plan (01:16)
- Intrusion Detection Policies (01:38)
- Who to Notify About an Incident (01:52)
- Recovery Operations (01:52)
- Other Operations (01:57)
- Forensic Investigation (03:04)
- Hacker/Penetration Methodology (05:40)
- Hacker/Penetration Methodology Continued (06:08)
- Summary (00:08)