Identity with Windows Server 2016, Part 5 of 6: Active Directory and Azure
with expert Patrick Loner
Course description
This course covers an understanding of how Azure AD and directory synchronization work. You will understand how to monitor the software for ongoing efficiency, CA types, and utilities within windows to provide the monitoring. This course finishes up with a discussion of certificate services and the foundation of public key infrastructure.
Prerequisites
This is part 5 of the series
Learning Paths
This course will help you prepare for the following certification and exam:
MCSA: Windows Server 2016
70-742: Identity with Windows Server 2016
This course is part of the following LearnNowOnline SuccessPaths™:
Windows Server 2016
Meet the expert
Patrick Loner has certifications for MCSA, MCSE, MCITP, A+, Network+, Security+, and more. He has been working as a Microsoft Certified Trainer, network administrator, and network consultant for over ten years. He has over a decade of experience working with and teaching about Windows networks with client and server operating systems. He has guided many students toward Microsoft and CompTIA certifications. Most recently, he has worked as a freelance trainer and network consultant specializing in Windows Server 2008 and Microsoft Exchange 2007 and Exchange 2010 implementations, design, and upgrades. Patrick continues to branch out now working with and training on Windows Server 2012, Windows 8, Exchange 2013, and System Center Configuration Manager 2012.
Course outline
Azure AD
Introduction to Azure AD (24:20)
- Introduction (00:25)
- Overview of Azure AD (05:39)
- Limitations of AD DS (02:37)
- Extending AD DS Authentication (03:35)
- Comparing AD DS and Azure AD (01:59)
- Authentication Options (04:54)
- Planning Directory Synchronization (02:57)
- Enabling AD DS Synchronization (02:03)
- Summary (00:08)
Implemeting Azure AD Connect (11:55)
- Introduction (00:11)
- What Is Azure AD Connect (01:51)
- Azure AD Connect Requirements (04:01)
- Azure AD Connect Express Settings (01:06)
- Azure AD Connect Custom Installation (02:06)
- Monitoring Azure AD (01:06)
- Privileged Identity Management (01:23)
- Summary (00:08)
Managing Identities with Directory Synch (06:24)
- Introduction (00:06)
- Managing Groups (00:56)
- Filtering Azure AD Connect (02:03)
- Monitoring Directory Synchronization (01:46)
- Troubleshooting Directory Synchronization (01:23)
- Summary (00:08)
Managing an AD DS Database
Monitoring AD DS (27:40)
- Introduction (00:22)
- Performance Monitoring Benefits (02:05)
- Establishing Performance Baselines (02:13)
- Introduction to Monitoring Tools (00:51)
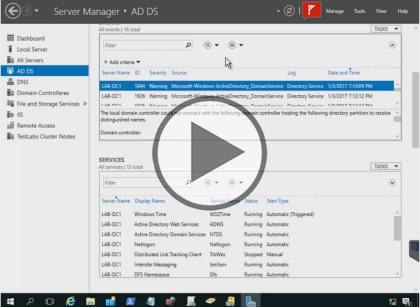
- Event Viewer (02:34)
- Demo: Event Viewer (05:12)
- Reliability Monitor (01:52)
- Real-Time Monitoring (02:42)
- Data Collector Sets (01:26)
- Data Collection Points (00:49)
- Common AD DS Counters (04:34)
- Best Practices (02:47)
- Summary (00:08)
Database Management (07:19)
- Introduction (00:08)
- Physical Data Store (03:00)
- Using NTDSUtil (02:36)
- AD DS Maintenance (01:26)
- Summary (00:08)
Backup and Recovery in AD DS (21:41)
- Introduction (00:12)
- Disaster Recovery for Active Directory (01:27)
- Backing Up Active Directory (04:17)
- Using Backup Tools (00:39)
- Backup Requirements (01:44)
- Restoring Data (04:27)
- Additional Restore Options (03:53)
- Demo: Enable AD Recycle Bin (03:23)
- Best Practices for Backup and Recovery (01:26)
- Summary (00:08)
Public Key Infrastructure
Overview of Public Key Infrastructure (17:02)
- Introduction (00:09)
- What Is a PKI (01:38)
- Encryption Types (02:05)
- PKI Components (01:56)
- PKI Enabled Applications (01:49)
- Certificate Authorities (01:45)
- CA Types (00:49)
- Internal vs. External CAs (03:24)
- AD CS in Windows Server 2016 (03:15)
- Summary (00:08)
Deploy Certificate Authority Hierarchy (19:07)
- Introduction (00:14)
- Decision Factors for CA Hierarchy (00:39)
- CA Hierarchy Roles (01:40)
- Best Practices for CA Hierarchies (01:22)
- Installing Root CAs (02:35)
- Demo: Set Up Root CA (03:47)
- Demo: Additonal Configuration (04:14)
- Subordinate CAs (02:26)
- Automating Installations (01:58)
- Summary (00:08)
Administering Certificate Authorities (13:24)
- Introduction (00:26)
- Administration Tools (03:09)
- Configuring CA Security (01:23)
- Security Roles for CA Administration (01:58)
- Policy and Exit Modules (01:29)
- Certificate Revocation List (02:37)
- Publishing the CRL (00:57)
- Publishing AIAs and CDPs (01:13)
- Summary (00:08)
Working With Certificates
Deploying and Managing Certificates (26:35)
- Introduction (00:09)
- Digital Certificates (01:55)
- Certificate Templates (01:08)
- Template Versions in Windows Server 2016 (02:11)
- Certificate Template Permissions (01:13)
- Updating Templates (01:20)
- Demo: Configure Certificate Template (05:44)
- Enrollment Types (02:02)
- Manual Enrollment (00:58)
- Automating Enrollment (01:33)
- Demo: Automatic Enrollment (02:19)
- Demo: Automatic Certificate Request (05:04)
- Credentials Roaming (00:47)
- Summary (00:08)
Manging Revocation and Distribution (07:01)
- Introduction (00:23)
- Certificate Revocation (01:25)
- Online Responder (01:41)
- Online Responder Process (00:51)
- Comparing CRL and OCSP (01:32)
- Configuring an Online Responder (00:59)
- Summary (00:08)
Configure Certificate Recovery (08:04)
- Introduction (00:17)
- Importance of Key Archival and Recovery (01:03)
- Key Archival (01:27)
- Data Revocery vs. Key Recovery (01:24)
- Archival and Export Methods (01:31)
- Automating Archival (01:01)
- Recovering Lost Keys (01:10)
- Summary (00:08)