Course description
Continue your exploration of SQL Server 2016 with a review of row level security, including a look at Always Encrypted and dynamic data masking, high availability, and clusters, and discover a wealth of enhancements in the areas of security and encryption.
Prerequisites
This course assumes that student has some familiarity SQL Server.
Learning Paths
This course is part of the following LearnNowOnline SuccessPaths™:
SQL Server Core
Meet the expert
Using Microsoft SQL Server started for Thomas with a Laboratory Information System in version 6.5. The Analysis Service (also called SSAS) option in version 7 got him excited about Data Warehousing, but before he used a production version of SSAS, he became a Database Administrator for versions 6.5 through 2005 while working at a paper mill and home health agency. After writing reports as an application developer for 10 years, he rediscovered Online Analytical Processing (OLAP) implemented into Data Warehouses. Since 2009, he has become a speaker in the SQL Server community and a voice for Microsoft Business Intelligence (MSBI) for enterprises. His transition from Sr. DBA to a Business Intelligence Architect has been a great career path. Thomas has certifications MCP, MCDBA and MCITP in Database Administration and Business Intelligence.
Course outline
Security and Availability
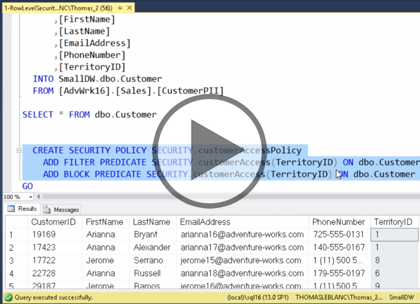
Row Level Security (16:56)
- Introduction (00:39)
- Overview (01:55)
- Row-Level Security (01:54)
- Filtered Predicate (01:58)
- Block Predicate (01:49)
- SCHEMABINDING (01:01)
- Restrictions (01:23)
- Demo: Row Level Security (05:33)
- Summary (00:41)
Always Encrypted (14:48)
- Introduction (00:38)
- Always Encrypted (05:46)
- Deterministic or Randomized (02:35)
- Demo: Always Encrypted (05:24)
- Summary (00:24)
Data Masking (15:00)
- Introduction (00:38)
- Data Masking (06:45)
- Demo: Data Masking (03:22)
- New Permissions (02:20)
- Encryption (01:23)
- Summary (00:29)
Clusters and Replication (16:14)
- Introduction (00:43)
- Overview (01:24)
- Clustering Updates (06:08)
- Replication (02:12)
- Always-On Availability Groups (01:21)
- Aways-On Continued (03:45)
- Summary (00:39)
Stretch Database (28:19)
- Introduction (00:38)
- Stretch Database (05:43)
- Demo: Stretch Database (03:48)
- Demo: Advisor (02:17)
- Database Stretch (02:16)
- Database Stretch Workflow (01:59)
- Partial Data Stretched (04:56)
- Database Stretch (05:51)
- Summary (00:46)