Course description
Becoming a computer forensic investigator requires not only time and effort, but also learning the necessary steps to follow in order to ensure a sound investigation. Take a closer look at the investigation process including what should be done before the investigation, during the investigation, and after the investigation to guarantee that your investigation is thorough, isn’t breaking any laws, and can be upheld should it be brought to court. This course is part of a series covering the EC-Council Computer Hacking Forensic Investigator (CHFI).
Prerequisites
Recommended:
Understanding of networking; How data flows from source and destination
Computer security basics such as passwords, encryption and physical security
Basic understanding of computing and computer systems
Experience with various operating systems
Learning Paths
This course will help you prepare for the following certification and exam:
Computer Hacking Forensic Investigator
Meet the expert
David Bigger is the lead trainer at Bigger IT Solutions. He has been information technology for a little over 20 years and has been training all over the US. He has worked with companies like US Military, Lockheed Martin, General Dynamics, Dominos Pizza, University of Utah and Expedia
Course outline
The Investigation Process
Before the Investigation (19:42)
- Introduction (00:26)
- Before the Investigation (02:13)
- The Investigation Team (03:37)
- The Lab Area (05:03)
- Our Forensic Workstation (03:57)
- Investigation Toolkit (04:05)
- Summary (00:19)
During the Investigation (33:54)
- Introduction (00:25)
- During the Investigation (01:32)
- Seizing and Searching (09:00)
- Collecting Evidence (00:26)
- Collecting Electronic Evidence (03:02)
- Collecting Physical Evidence (06:30)
- Securing the Evidence (01:22)
- Chain of Custody (02:49)
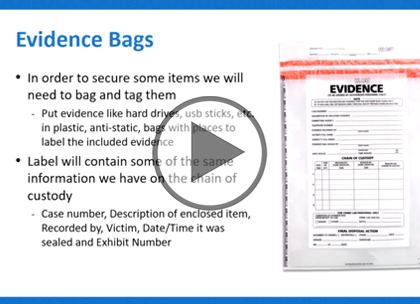
- Evidence Bags (01:29)
- The Logbook (00:57)
- Storing and Transporting (00:43)
- Acquiring the Data (00:29)
- Bit-for-Bit Copies (01:05)
- Verification of the Copy (00:40)
- Analyzing the Data (01:11)
- First Responders (01:44)
- Summary (00:23)
After the Investigation (15:34)
- Introduction (00:25)
- After the Investigation (00:50)
- Reporting (07:53)
- Being an Expert Witness (06:05)
- Summary (00:18)