Course description
This course discusses Cryptography, symmetric and asymmetric algorithms, public key cryptography and
Key Management. Next it covers hashing, steganography and how to manage Public Key infrastructure as well as digital certificates. Finally, it will go into detail around SSL and TLS, SSH and Virtual Private Networks for the SY0-501 Exam.
Prerequisites
• Basic familiarity with computer networks, administration, and security is helpful (But, all required information will be covered during the course)
• Completion of the CompTIA A+ and Network+ certifications (Helpful, but not required)
Meet the expert
Jason Dion, CISSP No. 349867, is a professor at University of Maryland University College with multiple information technology professional certifications, including Certified Information Systems Security Professional (CISSP), Certified Ethical Hacker (CEH), Certified Network Defense Architect (CNDA), Digital Forensic Examiner (DFE), Digital Media Collector (DMC), CySA+, Security+, Network+, A+, PRINCE2 Practitioner, and ITIL. He holds a Masters of Science degree in Information Technology with a specialization in Information Assurance
Course outline
Cryptography and PKI
Cryptography (25:02)
- Introduction (00:08)
- Cryptography (04:56)
- Symmetric vs Asymmetric (06:12)
- Symmetric Algorithms (04:57)
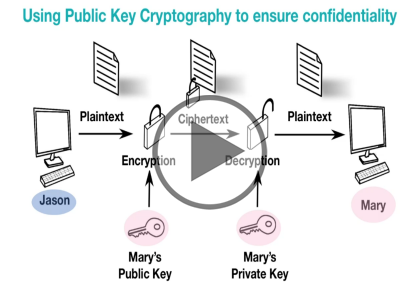
- Public Key Cryptography (03:09)
- Asymmetric Algorithms (03:44)
- Pretty Good Privacy (01:46)
- Summary (00:08)
Key Management (26:54)
- Introduction (00:08)
- Key Management (02:12)
- One-Time Pad (04:19)
- Demo: Steganography (03:51)
- Hashing (08:28)
- Demo: Hashing (03:04)
- Hashing Attacks (03:15)
- Increasing Hash Security (01:27)
- Summary (00:08)
Public key Infrastructure (21:12)
- Introduction (00:08)
- Public Key Infrastructure (03:53)
- Digital Certificates (06:43)
- Demo: Certificates (03:31)
- Certificate Authorities (04:13)
- Web of Trust (02:35)
- Summary (00:08)
Security Protocols (18:40)
- Introduction (00:08)
- Security Protocols (00:21)
- SMIME (01:30)
- SSL and TLS (05:48)
- SSH (02:28)
- VPN Protocols (06:38)
- Demo: Setting Up a VPN (01:37)
- Summary (00:08)