Course description
You made a new application last week, but is it secure? This course takes a look at Application security, specifically the things that might go wrong including Cross Side Scripting, SQL Injection attacks, and buffer overflows. But it won’t be all doom and gloom – this course will also take a look at some security frameworks and controls that can be put in place to better help protect applications from compromise. This course is part of a series covering the CompTIA Advanced Security Practitioner (CASP).
Prerequisites
This course assumes that the student has familiarity with information technology and basic networking. The student should also be familiar with basic security concepts, whether through the CompTIA Advanced Security Practitioner Parts 1-6 or outside study. No scripting or “hacking” experience is required.
Meet the expert
David Bigger is the lead trainer at Bigger IT Solutions. He has been information technology for a little over 20 years and has been training all over the US. He has worked with companies like US Military, Lockheed Martin, General Dynamics, Dominos Pizza, University of Utah and Expedia
Course outline
Assessments
Vulnerability Scans (25:53)
- Introduction (00:24)
- Assessments (02:59)
- Vulnerability Scans (04:03)
- Scans (05:32)
- When to Scan (06:43)
- Requirements (05:57)
- Summary (00:13)
Penetration Tests (14:49)
- Introduction (00:23)
- Penetration Test (02:32)
- Footprinting and Recon (04:07)
- Scanning (02:14)
- Enumeration (02:58)
- Hacking (02:16)
- Summary (00:17)
Assessment Tools (15:06)
- Introduction (00:22)
- Methods and Tools for Assessment (01:41)
- Port Scanners (02:19)
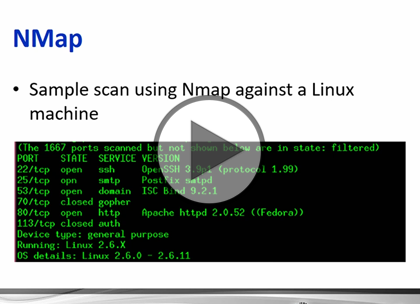
- NMap (01:10)
- Vulnerability Scanners (02:06)
- Password Crackers (02:43)
- Fuzzers (01:15)
- PsTools (01:37)
- Metasploit (01:33)
- Summary (00:15)