Course description
This courses discusses the importance of layer 2 security to the integrity of your network. Topics include: best practices, rogue devices, port security and ARP Spoofing.
Prerequisites
This is part 7 in the series.
Meet the expert
As a certified Microsoft Instructor, Ken has focused his career on various security aspects of computer and network technology since the early 1980s. He has offered a wide variety of IT training and high level consulting projects for Fortune 500 companies globally. Through the course of his extensive career, he has taught a full line of Microsoft, CompTIA, Cisco, and other high level IT Security curricula.
Course outline
Security
Security Best Practices (21:13)
- Introduction (00:12)
- OSI Layers Security (01:39)
- Layer 2 Security (02:39)
- Best Practices (09:50)
- Best Practices Continued (02:30)
- Rogue Devices (02:23)
- Layer 2 Attacks (01:48)
- Summary (00:08)
Port Security (32:45)
- Introduction (00:08)
- MAC Flooding eNotes (02:22)
- Port Security eNotes (01:54)
- Demo: Create Network (05:41)
- Demo: Port Security (05:21)
- Port Errors (03:00)
- Port-Based ACL (02:09)
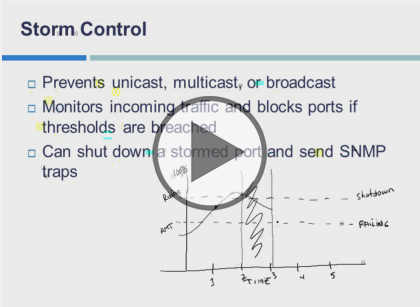
- Storm Control (02:56)
- Demo: Storm Control (02:18)
- AAA Framework (02:06)
- Authentication (03:02)
- RADIUS and TACACS (01:35)
- Summary (00:08)
RADIUS and TACACS (22:16)
- Introduction (00:08)
- RADIUS and TACACS+ (03:27)
- RADIUS and TACACS+ eNotes (02:57)
- Demo: AAA Configuration Options (04:36)
- Demo: AAA Groups (03:42)
- Limitations (01:19)
- Physical Security (01:26)
- 802.1x (00:59)
- 802.1x eNotes (01:40)
- 802.1x Configuration (01:49)
- Summary (00:08)
DHCP Spoofing (23:39)
- Introduction (00:08)
- DHCP Spoofing Attacks eNotes (03:12)
- Cisco DHCP Spoofing eNotes (01:42)
- IP Source Guard (01:33)
- ARP Spoofing eNotes (03:43)
- DAI (01:20)
- Dynamic Trunking Protocol (01:02)
- VLAN Hopping (02:59)
- VACLs (01:35)
- Why PVLANs eNotes (04:47)
- Isolated Ports (00:51)
- Protected Ports (00:34)
- Summary (00:08)